ISPs Should Do More to Safeguard the Web: FCC Chairman
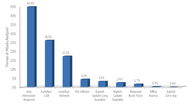
US Federal Communications Commission (FCC) chairman sought "smart, practical, voluntary solutions", without mandating his own, for internet service providers (ISPs) to fight online fraud and data theft. Chairman Julius Genachowski estimated that 8.4 million credit-card details are stolen online, each year. "If consumers lose trust in the Internet, this will suppress broadband adoption and online commerce and communication, and all the benefits that come with it," Genachowski said in a speech. The FCC feels ISPs can come up with solutions that prevent client PCs in the US from being forced into malicious botnets by hackers, without having to encroach upon users' privacy.
Genachowski urged ISPs to adopt DNSSEC, a system that ensures people accessing sensitive sites such as their banks' online transaction portals go to the right address, and not redirected to a fraudulent password phishing site. "To be effective, everyone who is a part of the Internet ecosystem must play a meaningful role in ensuring that private and government networks, and personal computers and devices are secured," said Comcast/NBCUniversal President Kyle McSlarrow in a blog posting. Comcast is one of America's biggest ISPs. This is an example of how threats to the sanctity of a productive internet can be defeated with highly-specific solutions that don't threaten privacy and freedoms, instead of broad-scoped legislations that potentially do.
Genachowski urged ISPs to adopt DNSSEC, a system that ensures people accessing sensitive sites such as their banks' online transaction portals go to the right address, and not redirected to a fraudulent password phishing site. "To be effective, everyone who is a part of the Internet ecosystem must play a meaningful role in ensuring that private and government networks, and personal computers and devices are secured," said Comcast/NBCUniversal President Kyle McSlarrow in a blog posting. Comcast is one of America's biggest ISPs. This is an example of how threats to the sanctity of a productive internet can be defeated with highly-specific solutions that don't threaten privacy and freedoms, instead of broad-scoped legislations that potentially do.