Thank you, right as you said I'm not up for correct terminology.What the heck is ASLR encryption? You do know ASLR is a randomization technique for addresss space layouts and doesn't have anything to do with encryption really, right?
-
Welcome to TechPowerUp Forums, Guest! Please check out our forum guidelines for info related to our community.
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
Intel Processors Hit with LVI Security Vulnerabilities, Mitigation Hits Performance Hard
- Thread starter btarunr
- Start date
Aquinus
Resident Wat-man
- Joined
- Jan 28, 2012
- Messages
- 13,236 (2.69/day)
- Location
- Concord, NH, USA
| System Name | Apollo |
|---|---|
| Processor | Intel Core i9 9880H |
| Motherboard | Some proprietary Apple thing. |
| Memory | 64GB DDR4-2667 |
| Video Card(s) | AMD Radeon Pro 5600M, 8GB HBM2 |
| Storage | 1TB Apple NVMe, 2TB external SSD, 4TB external HDD for backup. |
| Display(s) | 32" Dell UHD, 27" LG UHD, 28" LG 5k |
| Case | MacBook Pro (16", 2019) |
| Audio Device(s) | AirPods Pro, AirPods Max |
| Power Supply | Display or Thunderbolt 4 Hub |
| Mouse | Logitech G502 |
| Keyboard | Logitech G915, GL Clicky |
| Software | MacOS 15.5 |
I think @R-T-B's point is that If you're not getting the termanology right, what is supposed to make us think that you actually understand the problem correctly? So let's go through the steps you described:Thank you, right as you said I'm not up for correct terminology.
1. Unless you have root access to the machine, you're not going to know where the data your looking for is. So I don't understand how this is a realistic step in a real attack. You also need to know that this memory isn't going to change or move, so there are a lot of baked in assumptions here.
- We identify targets beforehand(this vulnerability is only the tool, not the means),
- We spoof memory,
- We disable cpu caching,
- We flush caches,
- We access memory first(this is very important to pull it off without concurrent programs reaching for their turn of memory),
- We pull spoofed memory which goes to L3,
- Our accessed memory is in the next sector, however collide+probe somehow makes the sectors enter "probe from access-violate next sector" which is in the next L3 page/word/tag(I haven't figured that part),
- Through magic voila we now have data that is 2^-15 the data we need.
2. What the heck is "spoofing memory"? Are you overwriting memory for something else? Don't you at least need root access to the machine to do that? Something like this would require ring-0 access on the VM host (not even ring -1 access from a VM,) to do something like that across bounds of a VM.
3. Ok, but do you have control to do that from a VM?
4. Ok, but still not sure if you can do this from a VM.
5. How do you plan on preventing that from happening? If it's a server, that's out of your control.
6. Once again, what is this "spoofing" you speak of? Writing to cache has the same kinds of constraints as writing to main memory and you're probably not doing this without ring 0 access.
7. What are you doing that forces the CPU to read from the next page page, word, or tag in cache? An access violation shouldn't scan for another item in cache, it should generate a machine check exception.
8.

- Joined
- Jul 5, 2013
- Messages
- 31,894 (7.26/day)
This sums it up. It's why I didn't respond. He doesn't seem to understand the context of the documentation, nor the practical application of the functionality of the construct of the proposed attack scenario. However, I'll give him credit for trying to understand it as he's putting in way too much effort to be trolling.I think @R-T-B's point is that If you're not getting the terminology right, what is supposed to make us think that you actually understand the problem correctly?
The part that I might have missed is this gentleman was speaking about Intel and told it right away that AMD was too contained with the addition of page attribution tables in zen+ generation. He kept on going at a spectre deliberation, but I couldn't delineate the two. Anyway, you word as good as mine, folks...
- Joined
- Jul 5, 2013
- Messages
- 31,894 (7.26/day)
AMD is completely unaffected by this new problem. The addressing system works a different way with everything AMD has made in the last 12 years. This is exclusively about Intel. At least that's what the data and documentation says.The part that I might have missed is this gentleman was speaking about Intel and told it right away that AMD was too contained with the addition of page attribution tables in zen+ generation. He kept on going at a spectre deliberation, but I couldn't delineate the two. Anyway, you word as good as mine, folks...
Aquinus
Resident Wat-man
- Joined
- Jan 28, 2012
- Messages
- 13,236 (2.69/day)
- Location
- Concord, NH, USA
| System Name | Apollo |
|---|---|
| Processor | Intel Core i9 9880H |
| Motherboard | Some proprietary Apple thing. |
| Memory | 64GB DDR4-2667 |
| Video Card(s) | AMD Radeon Pro 5600M, 8GB HBM2 |
| Storage | 1TB Apple NVMe, 2TB external SSD, 4TB external HDD for backup. |
| Display(s) | 32" Dell UHD, 27" LG UHD, 28" LG 5k |
| Case | MacBook Pro (16", 2019) |
| Audio Device(s) | AirPods Pro, AirPods Max |
| Power Supply | Display or Thunderbolt 4 Hub |
| Mouse | Logitech G502 |
| Keyboard | Logitech G915, GL Clicky |
| Software | MacOS 15.5 |
Sure, but even with hardware vulnerabilities, their usefulness has to be measured in practicality. Spectre is a great example of a vulnerability that has almost zero usefulness beyond an academic paper.The part that I might have missed is this gentleman was speaking about Intel and told it right away that AMD was too contained with the addition of page attribution tables in zen+ generation. He kept on going at a spectre deliberation, but I couldn't delineate the two. Anyway, you word as good as mine, folks...
I would advocate the contrary - meltdown is the more lethal vulnerability, but the easiest to patch. Spectre is different which makes it the benchmark vulnerability for this reason.Sure, but even with hardware vulnerabilities, their usefulness has to be measured in practicality. Spectre is a great example of a vulnerability that has almost zero usefulness beyond an academic paper.
I was transposing the commentary present for AMD to this argument. Have some sympathy!AMD is completely unaffected by this new problem. The addressing system works a different way with everything AMD has made in the last 12 years. This is exclusively about Intel. At least that's what the data and documentation says.

We should still keep comparing the two in my opinion cause lvi, as stated before, is pretty much theoretical only. It is a duel between amd spectre and intel spectre-class vulnerabilities.
- Joined
- Aug 20, 2007
- Messages
- 22,530 (3.44/day)
- Location
- Olympia, WA
| System Name | Pioneer |
|---|---|
| Processor | Ryzen 9 9950X |
| Motherboard | MSI MAG X670E Tomahawk Wifi |
| Cooling | Noctua NH-D15 + A whole lotta Sunon, Phanteks and Corsair Maglev blower fans... |
| Memory | 64GB (2x 32GB) G.Skill Flare X5 @ DDR5-6200(Running 1T no GDM) |
| Video Card(s) | PNY RTX 5080 OC |
| Storage | Intel 5800X Optane 800GB boot, +2x Crucial P5 Plus 2TB PCIe 4.0 NVMe SSDs, 1x 2TB Seagate Exos 3.5" |
| Display(s) | 55" Hisense 55U8N 4K FALD Display |
| Case | Thermaltake Core X31 |
| Audio Device(s) | TOSLINK->Schiit Modi MB->Asgard 2 DAC Amp->AKG Pro K712 Headphones or HDMI->B9 OLED |
| Power Supply | FSP Hydro Ti Pro 850W 80Plus Titanium PSU |
| Mouse | Logitech G305 Lightspeed Wireless |
| Keyboard | WASD Code v3 with Cherry Green keyswitches + PBT DS keycaps |
| Software | Gentoo Linux x64 / Windows 11 Enterprise (yes it's legit) |
AMD is completely unaffected by this new problem.
As far as we know. The docs are careful to state that AMD very well could and maybe even SHOULD be affected by this, they just could not make it happen in practice.
They state even in the white paper that you need meltdown for starters.As far as we know. The docs are careful to state that AMD very well could and maybe even SHOULD be affected by this, they just could not make it happen in practice.
- Joined
- Apr 1, 2008
- Messages
- 4,701 (0.74/day)
- Location
- Portugal
| System Name | HTC's System |
|---|---|
| Processor | Ryzen 5 5800X3D |
| Motherboard | Asrock Taichi X370 |
| Cooling | NH-C14, with the AM4 mounting kit |
| Memory | G.Skill Kit 16GB DDR4 F4 - 3200 C16D - 16 GTZB |
| Video Card(s) | Sapphire Pulse 6600 8 GB |
| Storage | 1 Samsung NVMe 960 EVO 250 GB + 1 3.5" Seagate IronWolf Pro 6TB 7200RPM 256MB SATA III |
| Display(s) | LG 27UD58 |
| Case | Fractal Design Define R6 USB-C |
| Audio Device(s) | Onboard |
| Power Supply | Corsair TX 850M 80+ Gold |
| Mouse | Razer Deathadder Elite |
| Software | Ubuntu 20.04.6 LTS |
They state even in the white paper that you need meltdown for starters.
If true, then AMD cannot be affected by this particular vulnerability.
- Joined
- Aug 20, 2007
- Messages
- 22,530 (3.44/day)
- Location
- Olympia, WA
| System Name | Pioneer |
|---|---|
| Processor | Ryzen 9 9950X |
| Motherboard | MSI MAG X670E Tomahawk Wifi |
| Cooling | Noctua NH-D15 + A whole lotta Sunon, Phanteks and Corsair Maglev blower fans... |
| Memory | 64GB (2x 32GB) G.Skill Flare X5 @ DDR5-6200(Running 1T no GDM) |
| Video Card(s) | PNY RTX 5080 OC |
| Storage | Intel 5800X Optane 800GB boot, +2x Crucial P5 Plus 2TB PCIe 4.0 NVMe SSDs, 1x 2TB Seagate Exos 3.5" |
| Display(s) | 55" Hisense 55U8N 4K FALD Display |
| Case | Thermaltake Core X31 |
| Audio Device(s) | TOSLINK->Schiit Modi MB->Asgard 2 DAC Amp->AKG Pro K712 Headphones or HDMI->B9 OLED |
| Power Supply | FSP Hydro Ti Pro 850W 80Plus Titanium PSU |
| Mouse | Logitech G305 Lightspeed Wireless |
| Keyboard | WASD Code v3 with Cherry Green keyswitches + PBT DS keycaps |
| Software | Gentoo Linux x64 / Windows 11 Enterprise (yes it's legit) |
They state even in the white paper that you need meltdown for starters.
You are correct. Mental failure, lol.
If true, then AMD cannot be affected by this particular vulnerability.
Right.
- Joined
- Jul 5, 2013
- Messages
- 31,894 (7.26/day)
While I'll admit my understanding of how L1/L2/L3 cache actually functions is limited, what I do know strongly suggests that Intel's and AMD's implementations differ enough that a vulnerability for one can not be assumed for the other.The docs are careful to state that AMD very well could and maybe even SHOULD be affected by this, they just could not make it happen in practice.
And then there's this.If true, then AMD cannot be affected by this particular vulnerability.
- Joined
- Aug 20, 2007
- Messages
- 22,530 (3.44/day)
- Location
- Olympia, WA
| System Name | Pioneer |
|---|---|
| Processor | Ryzen 9 9950X |
| Motherboard | MSI MAG X670E Tomahawk Wifi |
| Cooling | Noctua NH-D15 + A whole lotta Sunon, Phanteks and Corsair Maglev blower fans... |
| Memory | 64GB (2x 32GB) G.Skill Flare X5 @ DDR5-6200(Running 1T no GDM) |
| Video Card(s) | PNY RTX 5080 OC |
| Storage | Intel 5800X Optane 800GB boot, +2x Crucial P5 Plus 2TB PCIe 4.0 NVMe SSDs, 1x 2TB Seagate Exos 3.5" |
| Display(s) | 55" Hisense 55U8N 4K FALD Display |
| Case | Thermaltake Core X31 |
| Audio Device(s) | TOSLINK->Schiit Modi MB->Asgard 2 DAC Amp->AKG Pro K712 Headphones or HDMI->B9 OLED |
| Power Supply | FSP Hydro Ti Pro 850W 80Plus Titanium PSU |
| Mouse | Logitech G305 Lightspeed Wireless |
| Keyboard | WASD Code v3 with Cherry Green keyswitches + PBT DS keycaps |
| Software | Gentoo Linux x64 / Windows 11 Enterprise (yes it's legit) |
While I'll admit my understanding of how L1/L2/L3 cache actually functions is limited, what I do know strongly suggests that Intel's and AMD's implementations differ enough that a vulnerability for one can not be assumed for the other.
And then there's this.
As I admitted, I needed more caffiene/had a brain fart. Somehow got it confused with Spectre briefly.
- Joined
- Feb 3, 2017
- Messages
- 4,018 (1.30/day)
| Processor | Ryzen 7800X3D |
|---|---|
| Motherboard | ROG STRIX B650E-F GAMING WIFI |
| Memory | 2x16GB G.Skill Flare X5 DDR5-6000 CL36 (F5-6000J3636F16GX2-FX5) |
| Video Card(s) | INNO3D GeForce RTX™ 4070 Ti SUPER TWIN X2 |
| Storage | 2TB Samsung 980 PRO, 4TB WD Black SN850X |
| Display(s) | 42" LG C2 OLED, 27" ASUS PG279Q |
| Case | Thermaltake Core P5 |
| Power Supply | Fractal Design Ion+ Platinum 760W |
| Mouse | Corsair Dark Core RGB Pro SE |
| Keyboard | Corsair K100 RGB |
| VR HMD | HTC Vive Cosmos |
Not just caches, the microarchitectural implementation (and resulting behaviour) of various buffers that are attacked in recent vulnerabilities are different.While I'll admit my understanding of how L1/L2/L3 cache actually functions is limited, what I do know strongly suggests that Intel's and AMD's implementations differ enough that a vulnerability for one can not be assumed for the other.
Meltdown in particular seems to be a straightforward bug in Intel's design. One that is complex to abuse but still a bug.
Well, the explanation I've got from the expert is that this type of attack has no vector on AMD just because the PSP security processor does not have its own cache to be exploited like SGX.Not just caches, the microarchitectural implementation (and resulting behaviour) of various buffers that are attacked in recent vulnerabilities are different.
Meltdown in particular seems to be a straightforward bug in Intel's design. One that is complex to abuse but still a bug.
- Joined
- Apr 6, 2020
- Messages
- 73 (0.04/day)
| System Name | Carnival of Glass |
|---|---|
| Processor | Intel i9 14900K (previously 12900K/9900K, 8086K/Xeon X5670) |
| Motherboard | ASRock Z790 PG SONIC (Gigabyte Z690 Aorus Master, Gigabyte Z370 Aorus Gaming 7/390 Des/X58A-UD7) |
| Cooling | Corsair Hydro open loop, 480mm XR7, 360mm XR5! |
| Memory | 32GB Corsair Dominator 6000MT DDR5 @6466 CL36-38-38-72-114-2 |
| Video Card(s) | Zotac RTX 3090 w/Corsair XG7 block (previously 1080Ti/970) +200 core +800 RAM +shunt mod |
| Storage | 1x 2TB Samsung Evo 980 boot, 2TB Sabrent RQ, 2x2TB Crucial MX, 2x4TB WD SN850X, 16TB NAS! |
| Display(s) | Acer Nitro 27" 4K, Koorui 27" 2K144Hz Acer 24" 1080p LED, 65" and 55" 4K TVs |
| Case | Corsair 7000X (previously Corsair X570 Crystal SE) |
| Audio Device(s) | Onboard + EVGA Nu Audio Pro 7.1, Yamaha Y2K AV Amp, Rotel RX-970B + 4x Kef Coda IIIs :D |
| Power Supply | Corsair HX1500i Modular PSU |
| Mouse | Corsair Darkstar/M65/Logitech G502 Lightspeed (previously G600 MMO) |
| Keyboard | Corsair K70 Pro Optomech Axon, Logitech G910 Orion Spectrum (previously G19) |
| VR HMD | HTC Vive Cosmos x2 |
| Software | Windows 11 x64 Enterprise (legal!) |
| Benchmark Scores | https://www.3dmark.com/spy/18709841 https://valid.x86.fr/s9zmw1 https://valid.x86.fr/t0vrwy |
Everyone is still overlooking that a vulnerability much like Meltdown was found to attack AMD CPUs and a "RowHammer" type can attack anything with RAM+CPU so..only Virtual Machine hosts need poop themselves, maybe? Ah well, at least Intel's silicon is of higher quality and can handle its own current and voltage requirements.. In fact anything with a CPU and RAM should be nervous at this rate, my Oscilloscope is worried! The lines on the screen are all wavy.. Oh wait, it's supposed to do that! ^-^
Meltdown or spectre? Meltdown is more prolific and easier to debug. You just fence the user kernel from the system and all is well. Spectre is spoofing the system.a vulnerability much like Meltdown was found to attack AMD CPUs
Another overgeneralization. A row cycle takes what;a "RowHammer" type can attack anything with RAM+CPU
According to this Micron whitepaper, an All-Bank Refresh is issued an average of every 3.9µs and takes 295ns to complete.
Same Bank Refresh only requires that one bank in each bank group be idle in order for the command to process. The other 12 banks do not have to idle and can continue to operate normally.REFsb commands are issued every 1.95µs but complete in 130ns. Using REFsb reduces the impact on idle latency from 11.2ns to 5ns.
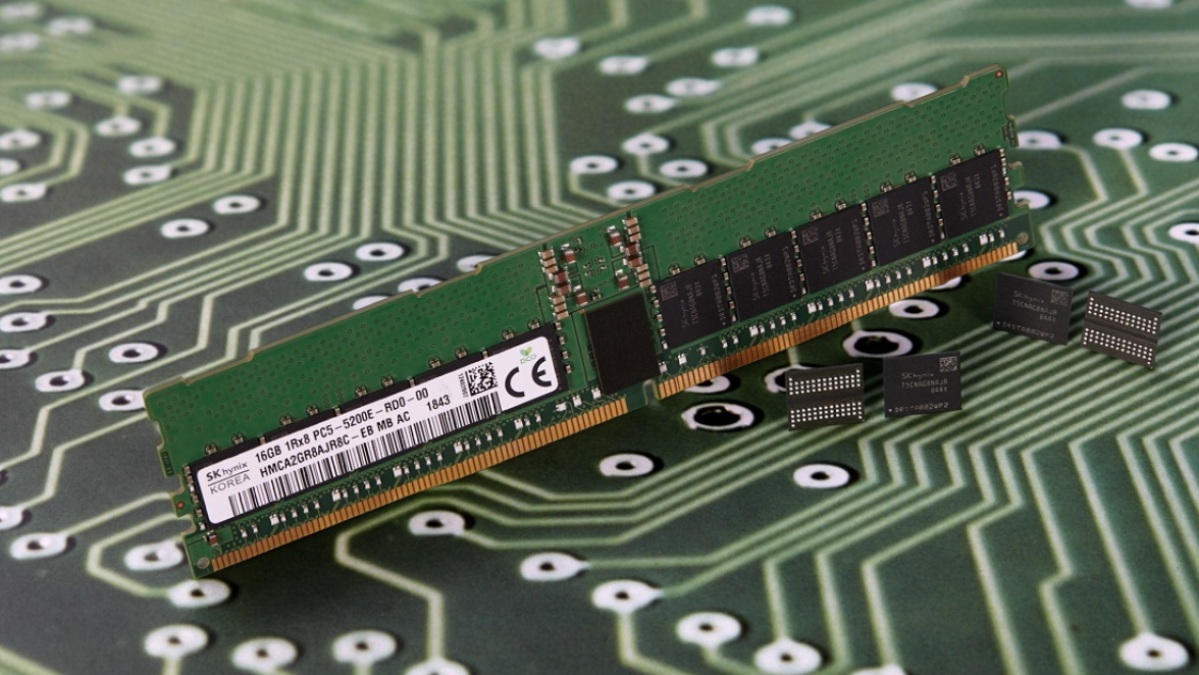
SK-Hynix Plans for Blazing-Fast DDR5-8400 PC Memory
SK Hynix has big plans for DDR5 and intends to extend the standard all the way to DDR5-8400.
- Joined
- Jul 5, 2013
- Messages
- 31,894 (7.26/day)
Except that you need physical access to exploit that one as well..Everyone is still overlooking that a vulnerability much like Meltdown was found to attack AMD CPUs and a "RowHammer" type can attack anything with RAM+CPU so..only Virtual Machine hosts need poop themselves, maybe? Ah well, at least Intel's silicon is of higher quality and can handle its own current and voltage requirements.. In fact anything with a CPU and RAM should be nervous at this rate, my Oscilloscope is worried! The lines on the screen are all wavy.. Oh wait, it's supposed to do that! ^-^


