ASUS Provides BIOS updates addressing MDS vulnerabilities, ZombieLoad, RIDL, and Fallout
ASUS is aware that a new sub-class of speculative execution side-channel vulnerabilities in Intel CPUs, called Microarchitectural Data Sampling (MDS), also known as ZombieLoad, RIDL, and Fallout, may allow information disclosure. Intel states that selected 8th and 9th Generation Intel Core processors, as well as the 2nd Generation Intel Xeon Scalable processor family, are not vulnerable to MDS. If you are using one of these processors, no further action is necessary.
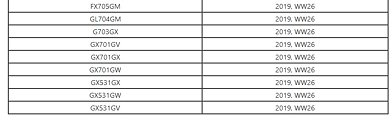
For other Intel processors, ASUS is working closely with Intel to provide a solution in a forthcoming BIOS update. We recommend owners of affected products update both the BIOS and operating system as soon as these mitigations are available. Please find our first-wave model list below and download the appropriate BIOS update from the ASUS Support website. More details, including affected systems, will be added to this document as they become available.
For other Intel processors, ASUS is working closely with Intel to provide a solution in a forthcoming BIOS update. We recommend owners of affected products update both the BIOS and operating system as soon as these mitigations are available. Please find our first-wave model list below and download the appropriate BIOS update from the ASUS Support website. More details, including affected systems, will be added to this document as they become available.