Monday, August 5th 2019

NVIDIA Issues Warning to Upgrade Drivers Due to Security Patches
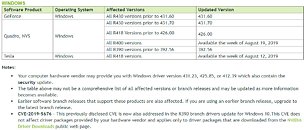
NVIDIA has found a total of five security vulnerabilities with its Windows drivers for GeForce, Quadro and Tesla lineup of graphics cards. These new security risks are labeled as very dangerous and have the potential to cause local code execution, denial of service, or escalation of privileges, unless the system is updated. Users are advised to update their Windows drivers as soon as possible in order to stay secure and avoid all of these vulnerabilities, so be sure to check your drivers for latest version. Exploits are only accessible on Windows based OSes, starting from Windows 7 to Windows 10.
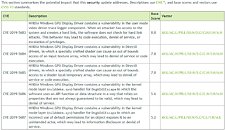
However, one fact that's reassuring is that in order to exploit a system, attacker must have local access to the machine that is running NVIDIA GPU, as remote exploit can not happen. Bellow are the tables provided by NVIDIA that show type of exploit along with rating it carries and which driver versions are affected. There are no mitigations for this exploit, as driver update is the only available solution to secure the system.The vulnerabilities are rated using CVSS V3 base scoring system and they are arranged as following:
However, one fact that's reassuring is that in order to exploit a system, attacker must have local access to the machine that is running NVIDIA GPU, as remote exploit can not happen. Bellow are the tables provided by NVIDIA that show type of exploit along with rating it carries and which driver versions are affected. There are no mitigations for this exploit, as driver update is the only available solution to secure the system.The vulnerabilities are rated using CVSS V3 base scoring system and they are arranged as following:
- CVE-2019-5683 - Most dangerous of all the vulnerabilities. This exploits uses driver's trace logger weakness to create hard links, that software does not check. Attacker could create any link without getting warned by the system and force local code execution, denial of service or escalation of privileges. It is rated with a score of 8.8.
- CVE-2019-5684 - Vulnerability which uses carefully crafted shaders in order to cause out of bounds access to input texture array, possibly leading to denial of service or code execution. It is rated with a score of 7.8
- CVE-2019-5685 - Vulnerability which also uses carefully crafted shaders in order to cause out of bounds access to shader local temporary array, possibly leading to denial of service or code execution as well. It is rated with a score of 7.8
- CVE-2019-5686 - Vulnerability hidden in kernel mode layer handler for DxgkDdiEscape, which uses different data structures and DirectX API functions that are not always valid, leading to denial of service if the API function or data structure is incorrect. It is rated with a score of 5.6.
- CVE-2019-5687 - Least dangerous exploit of all five. It is also a problem in kernel model layer handler for DxgkDdiEscape, which may put system at risk if incorrect default permissions are used for an object. This can lead to information disclosure or denial of service. It is rated with a score of 5.2.
32 Comments on NVIDIA Issues Warning to Upgrade Drivers Due to Security Patches
So basically the story will be if you want security roll AMD in full. Though I suspect they have issues just not found yet lol
This will straight up make them suicidal I recon.
www.zdnet.com/article/linus-torvalds-slams-cts-labs-over-amd-vulnerability-report/
Does it help NV?
Just think about it:
Intel: 100k employees
NVidia: 13k employees
AMD: 10k employees
We don't know about AMDs Spectre, Meltdown, Zombielend, BlueBazinga as well as, on GPU side of things, CVE-2019-1337, CVE-2019-1337-2, CVE-2019-1337-911 only because they simply lack the manpower to discover all that crap.
It is really unfair, when I think about it, one company simply doesn't give a flying Huang about discovering security issue and simply pretends to be secure, while others that do are deep in shit.
Very Bad! (c) Trump
Then they can use this exploit to execute code locally.
It's really terrifying stuff.
it's been a long time avoiding driver update, finally, I have to update the driver.
The whole idea behind trusted execution is that someone CAN write to your bios and get nowhere, really. The sigcheck fails (or should).Without admin rights, they can get admin rights.
That's the concern here.