Wednesday, May 15th 2019

Intel Releases CPU Microcode Updates For MDS Vulnerabilities Unearthed on May 14
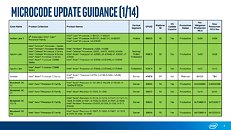
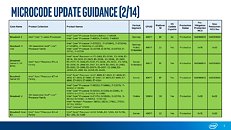
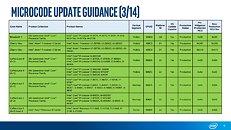
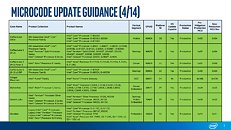
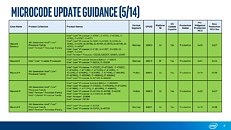
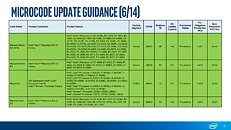
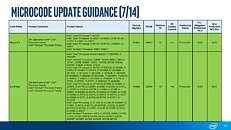
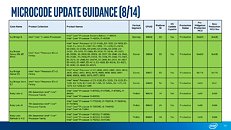
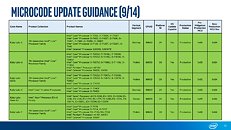
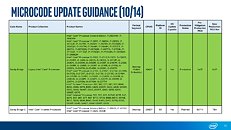
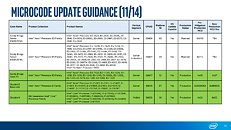
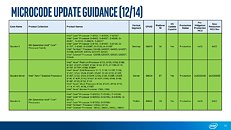
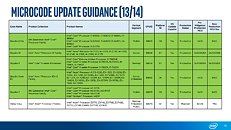
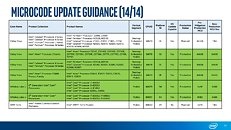
Intel released CPU microcode updates to address four new security vulnerabilities disclosed by the company on May 14, 2019. These microcode updates can be encapsulated as motherboard UEFI firmware updates, and for some processors even distributed through Windows Update. In its Microcode Revision Guidance document put out on Tuesday, Intel revealed that all Core and Xeon processors going as far as the 2nd generation Core "Sandy Bridge" architecture are eligible for microcode updates.
2nd generation Core is roughly the time when motherboard vendors were forced to adopt UEFI (unrelated to these vulnerabilities). A number of low-power microarchitectures, such as "Gemini Lake," "Cherry View," "Apollo Lake," and "Amber Lake," which are basically all low-power processors released after 2012-13, also receive these updates. Until you wait for your motherboard vendor or PC/notebook OEM to pass on these microcode updates, Intel advises you to disable HyperThreading if your processor is older than 8th gen "Coffee Lake," and seek out the latest software updates.Additional slides follow.
2nd generation Core is roughly the time when motherboard vendors were forced to adopt UEFI (unrelated to these vulnerabilities). A number of low-power microarchitectures, such as "Gemini Lake," "Cherry View," "Apollo Lake," and "Amber Lake," which are basically all low-power processors released after 2012-13, also receive these updates. Until you wait for your motherboard vendor or PC/notebook OEM to pass on these microcode updates, Intel advises you to disable HyperThreading if your processor is older than 8th gen "Coffee Lake," and seek out the latest software updates.Additional slides follow.
19 Comments on Intel Releases CPU Microcode Updates For MDS Vulnerabilities Unearthed on May 14
Select your OS version and then the most recent article.
I feel like I should run a benchmark or something before installing this. :P
en.wikichip.org/wiki/intel/cores/coffee_lake_r
en.wikichip.org/wiki/intel/cores/coffee_lake_s
Zombieload is too sensationalist and is best left to die, regardless of the fact the vulnerability is real. Scary names serve no one.
support.microsoft.com/en-us/help/4465065/kb4465065-intel-microcode-updates
Intel can put out whatever benchmark they want showing insignificant figures, I feel like this is them showing just the recent impact of a single patch and not the impact of all the patches combined. I want to see benchmarks of a fresh Win10 naked (completely free of any patches that have fixed all the recent Spectre flaws and whatever else you want to name) vs a Win10 fully patched.