Thursday, June 14th 2018

Intel Processors Hit by "Lazy FP State Restore" Vulnerability
Security researchers have discovered a vulnerability affecting all modern Intel Core and Xeon processors, which is an exploit of a performance optimization feature called "lazy FP state restore," which can be exploited to sniff out sensitive information, including cryptographic keys used to protect sensitive data. The flaw affects all x86 micro-architectures by Intel, "Sandy Bridge" and later.
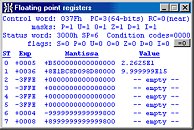
The "lazy FP state restore" feature is a set of commands used to temporarily store or restore the FPU states of applications running "lazily" (as opposed to "eagerly"). Red Hat put out an advisory stating that numbers held in FPU registers could be used to access sensitive information about the activities of other applications, including encryption keys. Intel began working with popular OS vendors to quickly roll out software patches against the vulnerability.
Sources:
Intel, Red Hat, TheHackerNews
The "lazy FP state restore" feature is a set of commands used to temporarily store or restore the FPU states of applications running "lazily" (as opposed to "eagerly"). Red Hat put out an advisory stating that numbers held in FPU registers could be used to access sensitive information about the activities of other applications, including encryption keys. Intel began working with popular OS vendors to quickly roll out software patches against the vulnerability.
43 Comments on Intel Processors Hit by "Lazy FP State Restore" Vulnerability
I'm more concerned about the router hack that is under FBI investigation right now...
If Intel are not careful, all those "massive" 3-6% improvements dating back the last 10 years or so will be gone, and we will be back to 2008 performance levels, with our shiny "new" and very expensive CPUs.
@btarunr, is there a link you can share?
Edit: Found one: www.phoronix.com/scan.php?page=news_item&px=Lazy-State-Restore-Spec-Exec
Edit 2: ...and this one: blog.cyberus-technology.de/posts/2018-06-06-intel-lazyfp-vulnerability.html
Note how neither of those links say anything about leaking encryption keys but rather just exposing FP register state. Is it a possible vulnerability, yes. Is it going to leak encryption keys? Probably not.
Just in time to release another CPU with the bug and go "lol, oops."
Software optimizations, in this case god knows what the software companies put in their bloatware anyway.
I am not saying this is definitely the case, but exploitable? Apparently yes.
Intel's fastest fancy million core Xeon CPU: 500 points
Any AMD CPU: 1200 points
As you can see, critical damage has been done to Intel.
As mentioned in the Red Hat source, these leaks can be used for one process to make assumption of the state of execution of another process. So it wouldn't leak actual sensitive data, but leak context. This sounds like an extreme edge case, but we'll see if they eventually find more "related" bugs that are actually serious. For a data leakage from a CPU to be useful, you would have to be able to target reading of specific memory addresses or similar, so you can slowly assemble sections of memory. If the data leaked is either uncontrollable or just general state information, then it's useless by itself, and probably in a larger context too.
Let me give another example of similar incorrect assumptions. Quite often we hear of new bugs in software where an attacker can cause a buffer overflow. Since a buffer overflow in theory can lead to arbitrary code execution, people usually automatically consider the bug serious and tell everyone to patch it immediately. In reality, "all" modern PCs have execute bit protection enabled which would stop any such exploit. But since there are still systems out there that may be vulnerable, this is automatically assumed critical, even though it's mostly limited to enterprise embedded systems, routers, legacy systems(>15 years). This very important distinction is almost always lost in the articles about the exploits.It's fairly common that one new bug gives researches ideas for new approaches of testing, and if a bug is due to incorrect assumptions, you can probably find more "related" problems. If you remember the software bug "Heartbleed", in the hysteria that followed, researchers found at least another 10 serious bugs. And people finding real bugs is a good thing.